Insights
/
feb 16, 2025
A Hacked Email Leads to a $190,000 Payment
Email account compromise can lead to fake invoices and fraudulent payments. Learn how attackers intercept emails and trick businesses into sending money.
/
AUTHOR
SolveCyber

Some of the most damaging cyber attacks don’t involve complex hacking techniques. Instead, attackers simply gain access to a company’s email account.
Once inside, they quietly monitor conversations, learn how the business operates, and wait for the right opportunity to commit fraud.
This type of attack is known as email account compromise, and it often leads to fake invoice scams that can cost businesses hundreds of thousands of dollars.
How the Scam Works
Attackers typically gain access to an email account through phishing or stolen passwords. Once inside, they can read previous conversations and understand how payments are handled.
When the timing is right, they send an email that appears completely legitimate — often pretending to be a supplier and requesting payment to new bank details.
Because the message comes from a real email account and includes genuine invoice information, it can be extremely difficult to detect.
A Real Example
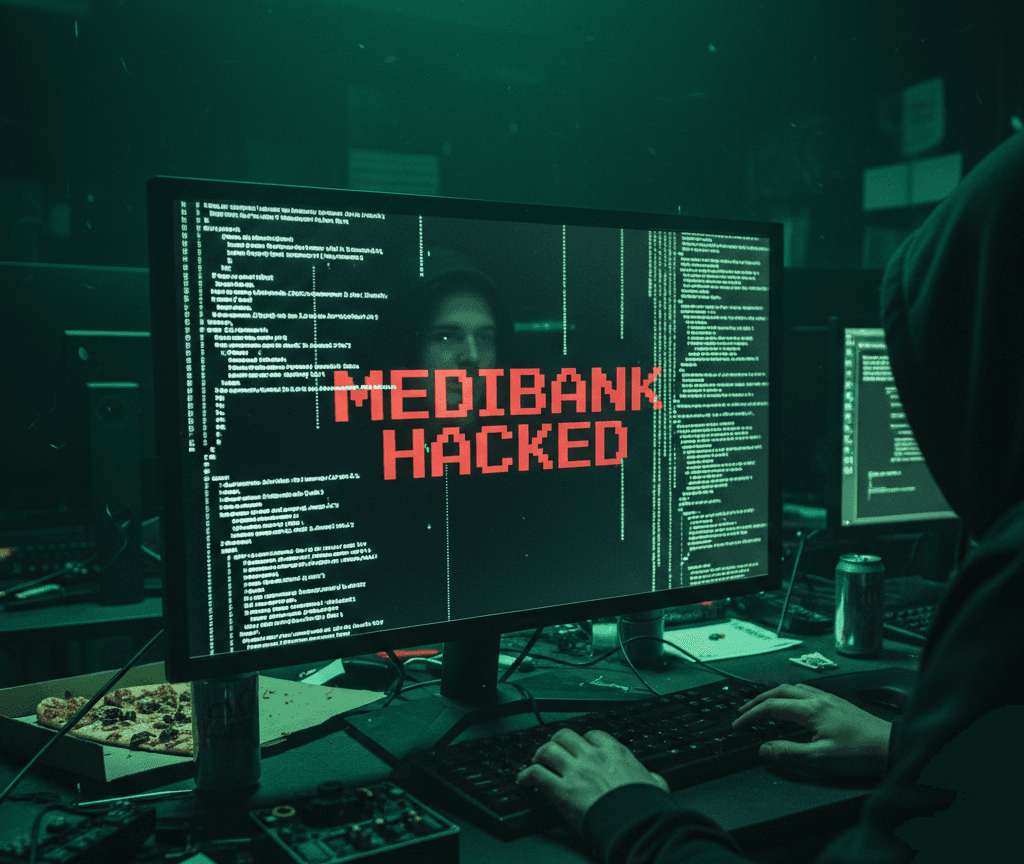
One business shared how they lost $190,000 after attackers compromised a supplier’s email account.
The attackers sent invoices that looked identical to previous ones, using the correct email address and even including the original email conversation. The only change was the bank account number.
Believing the request was genuine, the business transferred the payment.
The real supplier never received the money. The attackers had been intercepting emails and hiding the responses until the supplier eventually called to ask why the invoice had not been paid.
Why These Attacks Are So Dangerous
Invoice fraud works because it exploits trust and routine. When emails appear in genuine conversations and come from familiar contacts, small warning signs are easy to overlook.
By the time the fraud is discovered, the money is often gone.
How to Reduce the Risk
Email compromise attacks are common, but they can be prevented.
Security measures such as strong authentication, payment verification procedures, and employee awareness significantly reduce the risk.
Regular penetration testing can identify weaknesses attackers might exploit, while staff security training helps employees recognise suspicious payment requests before money is sent.