Insights
/
feb 16, 2025
The Biggest AWS Security Mistakes Companies Make
AWS provides powerful cloud infrastructure, but misconfigurations can create serious security risks. Learn the most common AWS security mistakes.
/
AUTHOR
SolveCyber
Moving to the cloud has become standard for many businesses. Platforms like Amazon Web Services offer reliable infrastructure, scalability, and strong built-in security features.
However, many organisations assume that using AWS automatically makes them secure.
In reality, most cloud security incidents are caused by configuration mistakes, not weaknesses in the platform itself.
Here are some of the most common AWS security mistakes companies make.
Publicly Exposed Storage Buckets
One of the most well-known cloud security issues involves Amazon S3, a storage service widely used for files, backups, and application data.
If permissions are configured incorrectly, an S3 bucket can become publicly accessible on the internet. This can expose sensitive information such as customer data, internal documents, or backups.
Many major data exposures have been caused by simple configuration errors like this.
Excessive Permissions
AWS uses a powerful identity system called AWS Identity and Access Management (IAM) to control who can access resources.
In many environments, however, users and applications are granted far more access than they actually need. Overly permissive roles can allow attackers to escalate privileges and gain control of additional resources if an account is compromised.
Following the principle of least privilege is critical to limiting damage during a security incident.
Exposed APIs and Services
Many applications hosted on AWS rely on APIs for communication between services.
If APIs are not properly secured, attackers may be able to access data or trigger functionality directly. This can lead to information exposure, unauthorised actions, or abuse of backend systems.
Because APIs are designed to be accessible, misconfigurations can easily go unnoticed.
Poor Network Configuration
AWS environments often contain multiple services communicating across internal networks.
Incorrect security group rules or open network ports can unintentionally expose internal services to the public internet. Attackers frequently scan cloud infrastructure looking for systems that were never intended to be publicly accessible.
Lack of Monitoring
Even well-configured environments require monitoring to detect suspicious activity.
AWS provides logging and monitoring tools such as AWS CloudTrail, but these are sometimes disabled or not reviewed regularly. Without proper logging, organisations may not realise an attacker has accessed their environment until much later.
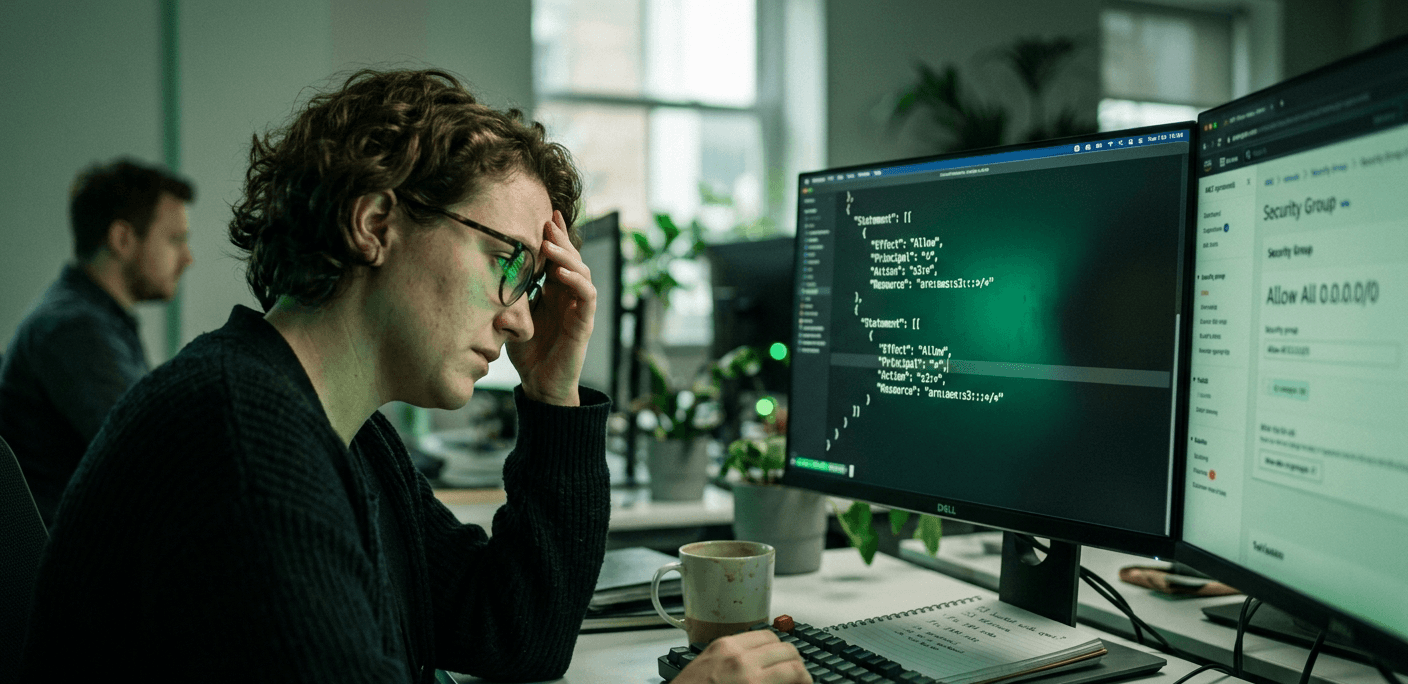
Why These Mistakes Happen
Cloud environments are powerful but complex. A typical AWS deployment may include dozens of interconnected services, each with its own permissions, networking rules, and configuration settings.
Small mistakes can create large security gaps, especially when systems are deployed quickly through automation or copied configuration templates.
Finding Cloud Security Risks
Because many AWS security issues are configuration-related, they can be difficult to detect without a thorough review.
Security assessments and penetration testing help identify misconfigured storage, excessive permissions, exposed services, and other weaknesses before attackers find them.
While AWS provides a secure foundation, the security of your environment ultimately depends on how it is configured and managed.