Insights
/
feb 16, 2025
The Real Cost of a Data Breach
Data breaches cost far more than most businesses expect. Learn the financial, operational, and reputational impact of a cyber incident.
/
AUTHOR
SolveCyber
When people think about a cyber attack, they often focus on the technical problem — a hacker gaining access to systems or data.
But the real damage usually comes after the breach is discovered.
Data breaches rarely affect just IT systems. They can disrupt operations, damage reputation, and create long-term financial consequences for the entire business.
Direct Financial Loss
One of the most obvious costs of a breach is the immediate financial impact.
Organisations may face expenses such as:
Incident response and forensic investigations
Legal and regulatory compliance costs
Customer notification and support
Security remediation and system recovery
In some cases, attackers may also steal funds directly or demand ransom payments.
These costs can escalate quickly, especially if large volumes of customer data are involved.
Regulatory and Legal Consequences
Businesses that store personal information may be required to report data breaches to regulators and affected individuals.
Investigations can lead to regulatory penalties, enforcement action, or class-action lawsuits. In many jurisdictions, organisations are legally required to demonstrate that they took reasonable steps to protect customer data.
Failure to do so can result in significant legal exposure.
Loss of Customer Trust
One of the most damaging consequences of a breach is the loss of trust.
Customers expect organisations to protect their personal information. When that trust is broken, it can lead to lost business, reduced customer loyalty, and long-term brand damage.
Rebuilding reputation after a breach can take years.
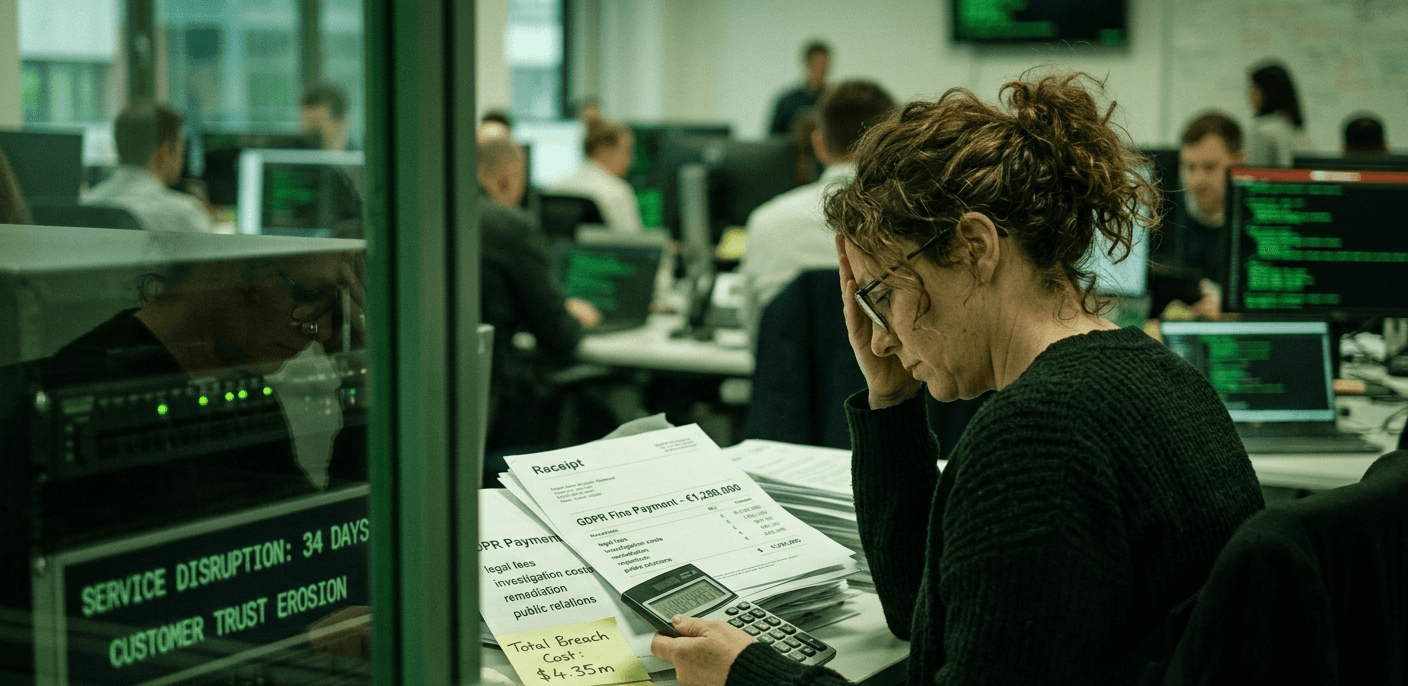
Operational Disruption
Cyber incidents often force organisations to shut down systems while investigations and remediation take place.
During this time, employees may lose access to critical tools, customers may experience service disruptions, and normal business operations can slow dramatically.
For some organisations, the operational impact can be just as damaging as the financial loss.
The Hidden Long-Term Costs
The true cost of a breach often continues long after the initial incident.
Businesses may need to invest heavily in new security controls, infrastructure upgrades, and compliance programs. Leadership time is consumed managing investigations, communications, and recovery efforts.
In many cases, the breach becomes a defining moment for the organisation.
Preventing the Next Breach
While no organisation can eliminate cyber risk entirely, proactive security measures significantly reduce the likelihood of a major incident.
Regular security assessments and penetration testing help identify vulnerabilities before attackers exploit them. Combined with strong security practices and staff awareness training, these steps provide one of the most effective ways to protect systems, data, and business reputation.